How To Know If You've Been a Victim of Shadow IT
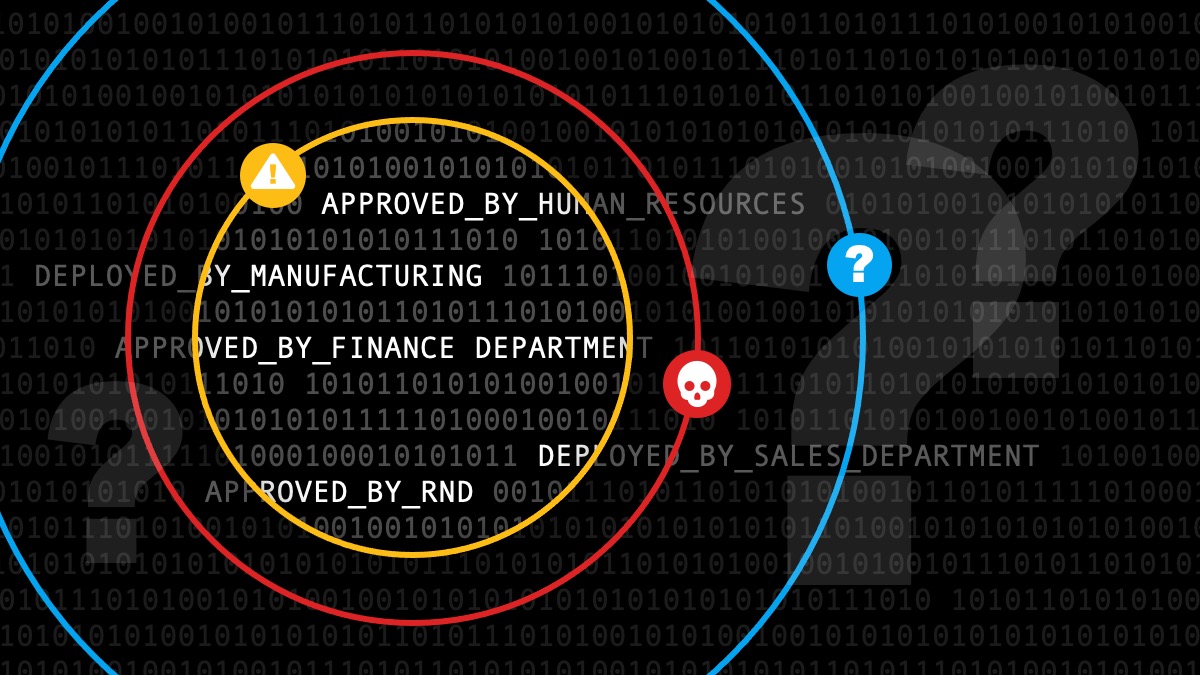
Shadow IT occurs when employees or departments adopt technology such as apps, software, or cloud tools, without the knowledge or approval of a centralized IT team. While the intent is usually positive, the lack of visibility and oversight can quietly increase cybersecurity, compliance, and business risk. In plain terms: employees choose tools to work fast and IT loses visibility. In the age of AI, this is rapidly becoming something you should be aware of.
Why Is Shadow IT so Common?
Modern work relies on fast, easy-to-use technology. Employees are more comfortable than ever installing apps, sharing files, and solving problems on their own. Cloud services and mobile apps make it possible to start using a tool in minutes, often without involving IT at all.
Research shows this behavior is widespread:
- Employees adopt unapproved tools (like AI) that bypass security controls
- Teams purchase technology directly and reduce IT involvement
IBM and Cisco both note that cloud-based tools and “sign in with Google” workflows have dramatically accelerated the growth of Shadow IT across organizations of all sizes.
How expanded access increases risk
Many organizations grant elevated system access so employees can work more flexibly. In some cases, this includes administrator privileges on work devices.
That convenience comes with tradeoffs:
- Admin access allows unrestricted installs which increases exposure
- Unvetted apps lac enterprise safeguards and raise the risk of a breach
- Free or consumer tools skip compliance standards and create blind spots
NIST guidance consistently recommends least‑privilege access, meaning users should only have the access required to do their job. Excess permissions expand the attack surface and increase the impact of mistakes or misuse.
Plot twist: Shadow It Isn't Always a Bad Thing
Not all aspects of Shadow IT are negative. In fact, it often signals innovation and unmet business needs.
Some positive outcomes are:
- Employees identify better tools that improve workflows
- Teams experiment with new platforms and drive innovation forward in your business
- You learn what users need and how to modernize your current systems
Technology adoption trends show that user-driven innovation is now a normal part of business evolution. Not a sign of poor behavior.
Basically, the challenge isn’t stopping Shadow IT entirely. The challenge is managing it responsibly.
3 Ways to Manage Shadow IT
Modern best practice focuses on visibility, standards, and education, not rigid restriction.
Maintain a Defined Technology Foundation
- Businesses should establish approved tools to maintain oversight
- Standard platforms reduce app sprawl and simplify security needs
Monitor for the Unknown
- Proactive monitoring detects unfamiliar apps and flags risk early
- Behavior analysis spots anomalies and limits damage
Educate Employees, Don't Blame Them
Human behavior is the leading factor in security incidents. Training turns employees into a line of defense instead of a risk factor.
According to the Center for Internet Security:
- Employee security awareness trainings improve threat recognition and reduces incidents
- Security awareness complements technical controls and strengthens security posture
Turn Shadow IT Into a Business Advantage
Shadow IT will continue to exist. Easy-to-use tools and fast-moving teams make it inevitable. The organizations that succeed are the ones that:
- Listen to employee needs
- Set clear technology standards
- Invest in visibility and security controls
- Treat education as risk reduction, not punishment
Think of it this way.
- Visibility enables protection
- Education reduces human risk
- Standards support flexibility
- Oversight protects long-term growth
Ready to start having an open conversation about Shadow IT? We can help. Let us know and we'll reach out today.